Tilman Baumgärtel, Julian Weinert: Van Gogh TV’s Piazza Virtuale: The Invention of Social Media at documenta IX in 1992 (2021)
Filed under book | Tags: · art, art history, internet, media art, social media, television

“Piazza virtuale by the group of artists known as Van Gogh TV was not only the biggest art project ever to appear on television, but from a contemporary point of view the project was also a forerunner of today’s social media. The ground-breaking event that took place during the 100 days of documenta IX in 1992 was an early experiment with entirely user-created content. This is the first book-length study of this largely forgotten experiment: it documents the radicality of Piazza virtuale‘s approach, the novel programme ideas and the technical innovations. It also allows, via QR codes, direct access to videos from the show, which until now have been inaccessible.”
Publisher transcript, Bielefeld, December 2021
Media Studies series, 96
Creative Commons BY-NC-SA 4.0 license
ISBN 3837660664, 9783837660661
231 pages
Research project website
Publisher
WorldCat
PDF, PDF (updated on 2023-7-31)
Comment (0)Inke Arns, Marie Lechner (eds.): Computer Grrrls (2021) [German/English]
Filed under catalogue | Tags: · algorithm, artificial intelligence, big data, cyberfeminism, hacking, internet, technofeminism, technology, women
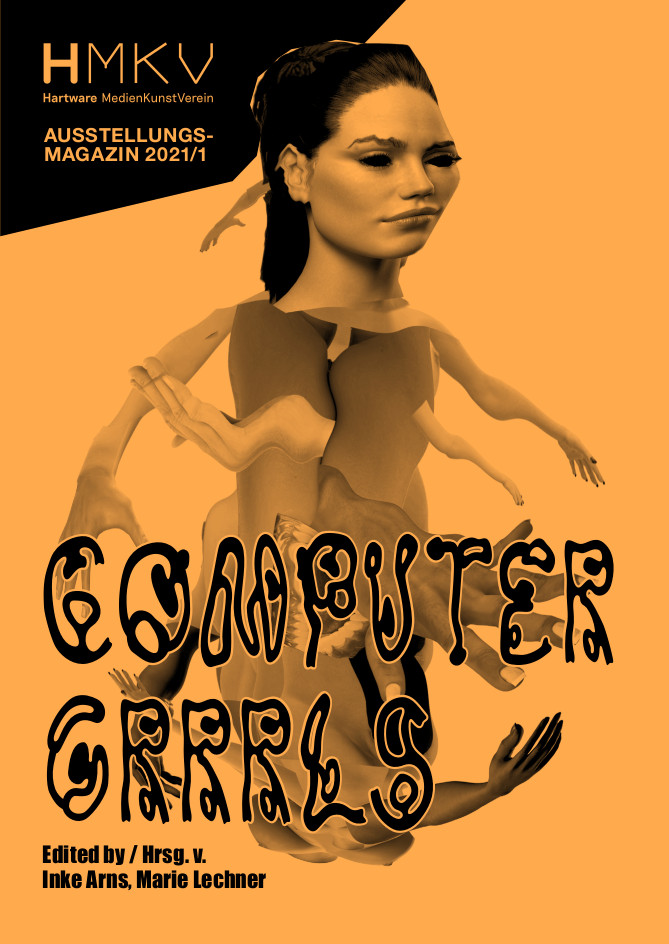
“Computer Grrrls brings together 23 international artistic positions that negotiate the complex relationship between gender and technology in past and present. The book deals with the link between women and technology from the first human computers to the current revival of technofeminist movements. An illustrated timeline with over 200 entries covers these developments from the 18th century to the present day.
The publication presents artists, hackers, makers and researchers who are working on how to think differently about technology: by questioning the gender bias in big data and artificial intelligence, promoting an open and diversified Internet, and designing utopian technologies.
The perspectives presented here address a broad range of topics: electronic colonialism, the place of minorities on the Internet, the sexist bias of algorithms, the dangerous dominance of white men in the development of artificial intelligence and digital surveillance, but also ideas on how we can change our traditional ways of thinking.
Artists included: Morehshin Allahyari, Manetta Berends, Zach Blas & Jemima Wyman, Nadja Buttendorf, Elisabeth Caravella, Jennifer Chan, Aleksandra Domanović, Louise Drulhe, Elisa Giardina Papa, Darsha Hewitt, Lauren Huret, Hyphen-Labs, Dasha Ilina, Roberte la Rousse, Mary Maggic, Caroline Martel, Lauren Moffatt, Simone C. Niquille, Jenny Odell, Tabita Rezaire, Erica Scourti, Suzanne Treister, Lu Yang.”
Publisher Kettler, Dortmund, and HMKV, Dortmund, May 2021
Open access
ISSN 2629-2629
ISBN 9783862069071
191 pages
HT coco
Publisher
Publisher
Exhibition (HMKV, 2018-2019)
PDF, PDF (59 MB, updated on 2024-8-27)
Comment (0)Legacy Russell: Glitch Feminism: A Manifesto (2020)
Filed under book | Tags: · body, cyberfeminism, feminism, gender, glitch, internet, race, technology, women
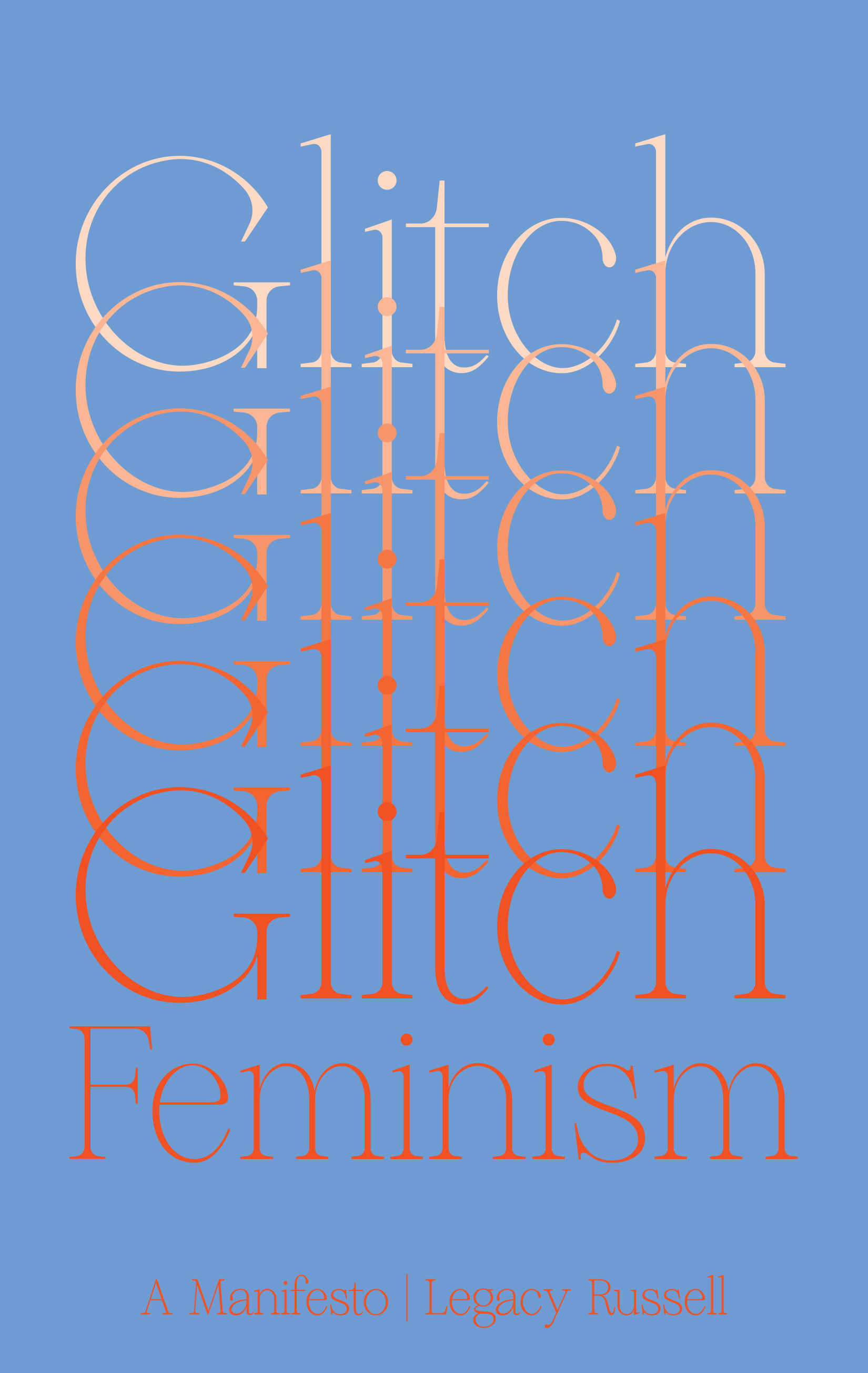
“Simone de Beauvoir said, “One is not born, but rather becomes, a woman.” The glitch announces: One is not born, but rather becomes, a body.
The divide between the digital and the real world no longer exists: we are connected all the time. What must we do to work out who we are, and where we belong? How do we find the space to grow, unite and confront the systems of oppression? This conflict can be found in the fissures between the body, gender and identity. Too often, the glitch is considered a mistake, a faulty overlaying, a bug in the system; in contrast, Russell compels us to find liberation here. In a radical call to arms, Legacy Russell argues that we need to embrace the glitch in order to break down the binaries and limitations that define gender, race, sexuality.
Glitch Feminism is a vital new chapter in cyberfeminism, one that explores the relationship between gender, technology and identity. In an urgent manifesto, Russell reveals the many ways that the glitch performs and transforms: how it refuses, throws shade, ghosts, encrypt, mobilises and survives. Developing the argument through memoir, art and critical theory, Russell also looks at the work of contemporary artists who travel through the glitch in their work. Timely and provocative, Glitch Feminism shows how an error can be a revolution.”
Publisher Verso, London, September 2020
ISBN 9781786632661, 1786632667
176 pages
Reviews: Rahel Aima (Bookforum, 2020), R.V. Campbell (The White Review, 2020), Johanna Marie Engemann (re:visions, 2020, DE), Ondřej Trhoň (Revue Prostor, 2020, CZ), Pauline Nguyen (Femme Art Review, 2021), Miranda Findlay (Feminist Formations, 2021), O.K. Keyes (Studies in Art Education, 2021), Hannah Curran-Troop & Annelot Prins (Eur J Cult Stud, 2022), Zoe Hurley (Postdigital Sci & Edu, 2023), Ondřej Trhoň (Artalk.cz, 2023, CZ).
Interviews with author: Mikkel Rosengaard (Bookforum, 2020), Ben Davis (artnet, 2020), ATM (2020), William Kherbek (Berlin Art Link, 2020).
PDF (updated on 2023-10-23)
Comment (0)